Risk Management
Basic policy on risk management
SuMi TRUST Group follows a basic policy of accurately assessing risk conditions and implementing necessary measures through a series of risk management activities, including risk identification, evaluation, monitoring, control and mitigation, based on the Group’s management policy and basic policy on the internal control system. Our Group’s risk management framework encompasses the Risk Appetite Framework and is linked to functions organically within the Group.
Risk management system
(1) Risk governance system
For the group-wide risk governance system, the Group has developed a Three Lines of Defense system consisting of risk management by individual Group businesses (first line of defense), risk management by the Risk Management Department and individual risk management-related departments (second line of defense) and validation by Internal Audit Department (third line of defense).
Risk governance system

(i) First line of defense
Each Group business identifies and gains an understanding of the risk characteristics involved in carrying out its own business, based on knowledge of the services and products in that business. Each Group business takes risks within the scope of its risk appetite in accordance with its risk-taking policy, evaluates risks and swiftly implements risk control at the on-site level when risks that are outside of its risk appetite materialize. In addition, the status of risk management is reported to the second line of defense in a timely manner.
(ii) Second line of defense
In accordance with the Group-wide basic policy on risk management approved by the Board of Directors, as control departments responsible for the management of each risk category, the Risk Management Department and risk management-related departments perform a check and balance function for the risk taking of the first line of defense, and supervise and provide guidance regarding the risk governance system from an independent standpoint.
The Risk Management Department, as an enterprise risk management department identifies and evaluates groupwide risks, creates a risk management process and sets risk limits. In addition, it formulates group-wide recovery strategies, in advance, to prepare for cases when risks materialize. Furthermore, it shares information with risk management-related departments appropriately, monitors the overall status of risks and risk management in an integrated manner and reports the status to the Executive Committee and the Board of Directors.
(iii) Third line of defense
The Internal Audit Department audits the effectiveness and appropriateness of the group-wide risk governance system and processes from a standpoint independent of the first and second lines of defense.
(iv) Executive Committee
The Executive Committee is composed of representative executive officers and executive officers designated by the President. It makes decisions on matters concerning risk management and undertakes preliminary discussions regarding matters to be resolved by and reported to the Board of Directors.
(v) Board of Directors
The Board of Directors is composed of all of the directors. It decides on the Group’s management policy and strategic goals for risk taking, formulates a risk management policy that reflects these strategic goals based on a solid understanding of where and what risks exist, and develops an appropriate risk governance system and supervises its implementation. The Board of Directors has voluntarily established the Risk Committee and the Conflicts of Interest Committee as advisory bodies based on the business strategies and risk characteristics of the Group.
Risk Committee
The Risk Committee receives requests for consultation from the Board of Directors on matters concerning the recognition of the environment surrounding the Group and the effectiveness of its risk management reviews their appropriateness, and reports its findings.
Conflicts of Interest Committee
The Conflicts of Interest Committee receives requests for consultation from the Board of Directors on matters concerning the Group’s fiduciary duties and conflicts of interest management, which are the foundation on which the Group seeks to become the “Best Partner” of its clients based on a fiduciary spirit, reviews their appropriateness, and reports its findings.
(2) Risk management process
In the Group, the Risk Management Department and individual risk management-related departments act as the second line of defense, performing risk management using the following procedure. This risk management process, along with its associated systems, undergoes regular auditing by the Internal Audit Department, which acts as the third line of defense.
(i) Risk identification
The risks faced by the Group are comprehensively identified, while ensuring the comprehensiveness of the Group’s operations, and the risks to be managed are identified based on the size and characteristics of the identified risks. Among those risks, risks that are particularly important are managed as material risks.
(ii) Risk evaluation
The risks identified as requiring management undergo analysis, evaluation, and measurement in a manner appropriate for the scale, characteristics, and risk profiles of each of the Group’s businesses. Among those risks, we periodically evaluate material risks in terms of the frequency of occurrence, degree of impact and severity to determine whether they can be classified as “top risks” (risks that require management attention due to their potential to have a material impact on the Group’s business capabilities and earnings targets within one year) or “emerging risks” (risks that could have a material impact in the medium to long term; i.e., after one year).
(iii) Risk monitoring
After setting KRIs*1 and other indicators, risk conditions are monitored with appropriate frequency, given the conditions of the Group’s internal environment (risk profiles and allocated capital usage status) and external environment (the economy and markets). Recommendations, guidance and advice are given to each of the Group’s businesses based on the risk conditions. Monitoring results are reported and submitted for proposal to the Board of Directors, the Executive Committee and other bodies regularly or as needed.
*1KRI = Key Risk Indicator
Risk predictor management for top risks
We select top risks, emerging risks, and others, based on the features of the business model and risk characteristics of the Group. We set risk appetite indicators for risks resulting from internal factors and early warning indicators for risks resulting from external factors for monitoring purpose.
Main top risks and emerging risks
- Risks related to falling prices for strategic shareholdings
- Risks related to concentration of credit in major obligors in the credit portfolio
- Risks related to cyber-attacks
- Risks related to climate change*2
- Risks related to the manifestation of geopolitical risk (e.g., the Ukraine crisis)
- Risks related to innovation
- Risks related to Japan’s declining birthrate and aging population
*2For more information on the Group’s initiatives to address climate change-related risks, please refer to “Climate change response” (on p.34) in this report and the TCFD Report (published in December 2022).
(iv) Risk control and mitigation
If any events that could have a significant impact on the soundness of management occur, such as risk amounts exceeding the acceptable range of risk appetite or risk limits, or the existence of concerns that it might do so, appropriate reports are presented to the Board of Directors, the Executive Committee and other bodies, and the necessary countermeasures are implemented according to the severity of the risk.
Risk appetite
(1) Outline of the Risk Appetite Framework
The Risk Appetite Framework is a group-wide corporate management framework consisting of the process for determining risk appetite within the Group’s risk capacity, together with an internal control system that monitors the process and ensures its appropriateness and sufficiency, in order to achieve management strategies formulated based on the Group’s Purpose, Mission (management principles), materiality and others.
With the primary objective of balancing improvement in profitability with enhancement of risk management, our Group’s Risk Appetite Framework establishes communication processes through the setting, propagation, and monitoring of risk appetite and promotes the improvement of transparency in the decision-making process, the optimization of the allocation of management resources, and the strengthening of the monitoring system for risk-taking overall. Through the above, the Group is promoting the enhancement of risk governance, which forms a part of corporate governance, with the aim to achieve sound and sustainable development through the value creation process by implementing and enhancing the Risk Appetite Framework.
Outline of the Risk Appetite Framework

(2) Risk appetite operation
(i) Determining risk appetite target
Our Group classifies risks into two categories: (1) risks to be taken (that occurs in relation to activities that generate returns) and (2) risks to be avoided (such as conduct risk that cannot be tolerated by the Group).
Under the Group’s Risk Appetite Framework, the Board of Directors establishes a risk-taking policy, based on Purpose and others, and sets risk appetite indicators taking the results of stress tests into account. In addition, the Executive Committee sets a detailed risk-taking policy and risk appetite indicators for each business type within the scope of the policy set by the Board of Directors.
The Group maintains the Risk Appetite Statement to clarify the overall picture, policy, and indicators of the Risk Appetite Framework.
The risk-taking policy and risk appetite indicators are determined in a manner consistent with the management plan, and are reviewed at least once a year or when necessary.
(ii) Risk appetite monitoring
Our Group sets risk appetite indicators from the three perspectives of return, risk, and cost, and regularly monitors and verifies that risk taking is conducted appropriately. In addition, we set risk appetite indicators for each materiality to monitor actions to address material issues in order to ensure that the value creation process is functioning appropriately, and that financial and non-financial capital are circulating.
If the risk appetite indicators deviate from the set levels, the Group analyzes the cause and implements countermeasures or reconsiders the levels of risk taking.
Fostering and instilling a risk culture
Our Group defines risk culture as a basic philosophy that prescribes the codes, attitudes, and conduct of the Group’s organizations, as well as its directors, officers and employees, that flexibly execute risk taking, risk management and risk control based on an appropriate assessment of risks, guided by a high degree of self-discipline based on a fiduciary spirit.
We define risk-taking policies for each Group business when formulating its management plan, and encourage appropriate risk-taking by all directors, officers and employees. In this way, the Group aims to build sustainable business models that contribute to enhancing corporate value and stakeholder value, and strives to get risk culture understood and embraced through e-Learning and discussion-based training to foster risk culture and get it rooted across the Group.
Risk characteristics
Based on a fiduciary spirit, and leveraging its significant expertise and comprehensive capabilities, the Group, as a trust group, strives to create distinct value through a total solution business model that combines its banking, asset management and asset administration, real estate businesses and others.
Each of the Group’s businesses faces various risks, including credit risk, market risk, funding liquidity risk and operational risk, depending on its business characteristics.
In this context, as a basis for improving management of risks related to trust business operations, we have established the Group-wide Trust Business Guidelines to provide information about basic matters that warrant caution. SuMi TRUST Bank primarily manages these risks in the operational risk category, particularly in terms of its duty of due care as a prudent manager, duty of loyalty and duty to segregate property as a trustee.
With regards to conduct risk as well, SuMi TRUST Bank, which is the core of the Group, periodically assesses the status of major risks and strives to promote and foster awareness among directors, officers and employees through internal training, thereby reducing and managing risks and preventing them from materializing.
Enterprise risk management
(1) Enterprise risk management system
We manage risks by comprehensively ascertaining the risks faced by the Group, which are evaluated on an individual risk category basis, and comparing and contrasting them against our corporate strength, i.e., capital adequacy (enterprise risk management).
We evaluate the effectiveness of our risk management and risk control annually, and when a need arises due to changes in the business environment or other circumstances, we will consider revisions to our risk category system, risk management system and other policies.
Among the risks we manage through our enterprise risk management, we aggregate risks that can be quantitatively measured using a single yardstick, such as VaR*, and compare the aggregated risk value against our corporate strength, i.e., capital adequacy, thereby managing risks (integrated risk management).
*VaR = Value at Risk.
(2) Capital allocation operations
For the purpose of the Group’s capital allocation operations, SuMi TRUST Holdings allocates capital to each Group business for each risk category (credit risk, market risk and operational risk) in consideration of the external environment, risk-return performance status, scenario analysis and the results of assessment of capital adequacy level.
The capital allocation plan is subject to the approval of the Board of Directors. Capital allocation levels are determined based on the Group's risk appetite.
Each Group business is operated within both the allocated amount of capital and the risk appetite. The Risk Management Department measures risk amounts on a monthly basis, and reports regularly on the risk status, compared to the allocated capital and risk appetite, to the Board of Directors and others.
(3) Stress tests and assessment of capital adequacy level
The Risk Management Department performs three types of stress tests (hypothetical scenario stress testing, historical scenario stress testing and examination of probability of occurrence) each time a capital allocation plan is formulated or reviewed, with the aim of ensuring capital adequacy from the standpoint of depositor protection. Based on the results of these stress tests, it assesses the level of capital adequacy, and reports to the Board of Directors and others.
Crisis management
Our Group strives to develop systems to swiftly and appropriately implement measures in the event of disasters, large-scale computer system failures, outbreaks of new infectious diseases, and the like, which are rooted in its public mission and social responsibilities as a financial institution.
In the event of a crisis, an emergency response headquarters led by the President will be established to ensure the safety of our clients, directors, officers, employees and their families as a top priority. Further, we have BCPs (business continuity plans) in place to continue to provide services in the event of a crisis.
In order to ensure the effectiveness of our BCPs, we periodically conduct exercises and revise their content. In particular, we have been working to develop and enhance alternative systems, such as backup offices and backup systems, to prepare for large-scale disasters. In order to prepare for the outbreak and spread of new infectious diseases, we are striving to prevent the spread of infection and maintain our functions as a social infrastructure by using our experience in dealing with the COVID-19 pandemic such as further enhancing and utilizing the teleworking environments.
New product and service examination system and post-introduction management system
When introducing a new product or service, it is necessary to develop various systems in order to continue offering the product or running the operation, including making an advance determination regarding the existence of any inherent risks and identifying their types, evaluating and managing such risks, and developing materials and methods for explanation to clients. To that end, we have developed a new product and service examination system. In the examination process, multiple departments carry out verification from various angles, with an emphasis on introducing products and services that will earn the trust of clients.
For products and services that have been examined by the Product Examination Committee, after they are introduced, we regularly monitor the status of our post-introduction initiatives, including from a risk management perspective.
Regular monitoring is also carried out from the viewpoint of providing clients with appropriate explanations for products and services that are expected to be affected due to changes in the environment and so on, regardless of whether or not they have been deliberated on by the Product Examination Committee.
Product examination process (SuMi TRUST Bank)
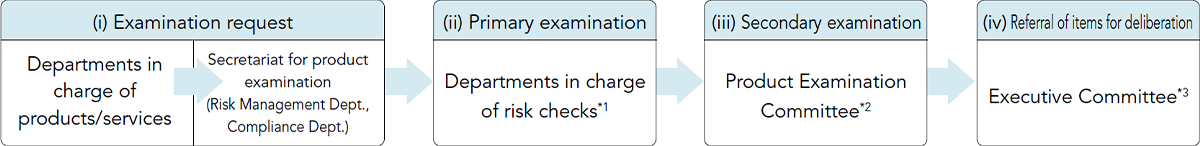
*1Risk Management Dept., Compliance Dept., Legal Dept., Planning and Coordination Dept., Fiduciary Duties &anp; Customer Satisfaction Planning and Promotion Dept., Financial Planning Dept., Business Process Planning Dept
*2Held jointly with the Conflicts of Interest Management Enhancement Committee as necessary to review from the perspective of conflicts of interest in light of merchantability.
*3When new products and services that may have a material impact on the Group’s management are referred to SuMi TRUST Bank’s Executive Committee, consultation with SuMi TRUST Holdings is required, and a framework is provided for bringing up matters at the Executive Committee and reporting to the Board of Directors.
Please refer to the Qualitative Disclosure Data: SuMi TRUST Holdings (page 216-247) for information on the risk management of SuMi Trust Group.
